Network Security with NordLayer – Secure Remote Access for Modern Businesses
The traditional office perimeter no longer exists.
Employees work remotely. Teams connect from home networks, airports, cafés, and shared spaces. Cloud services replace local infrastructure. And every new access point becomes a potential vulnerability.
That’s where NordLayer comes in.
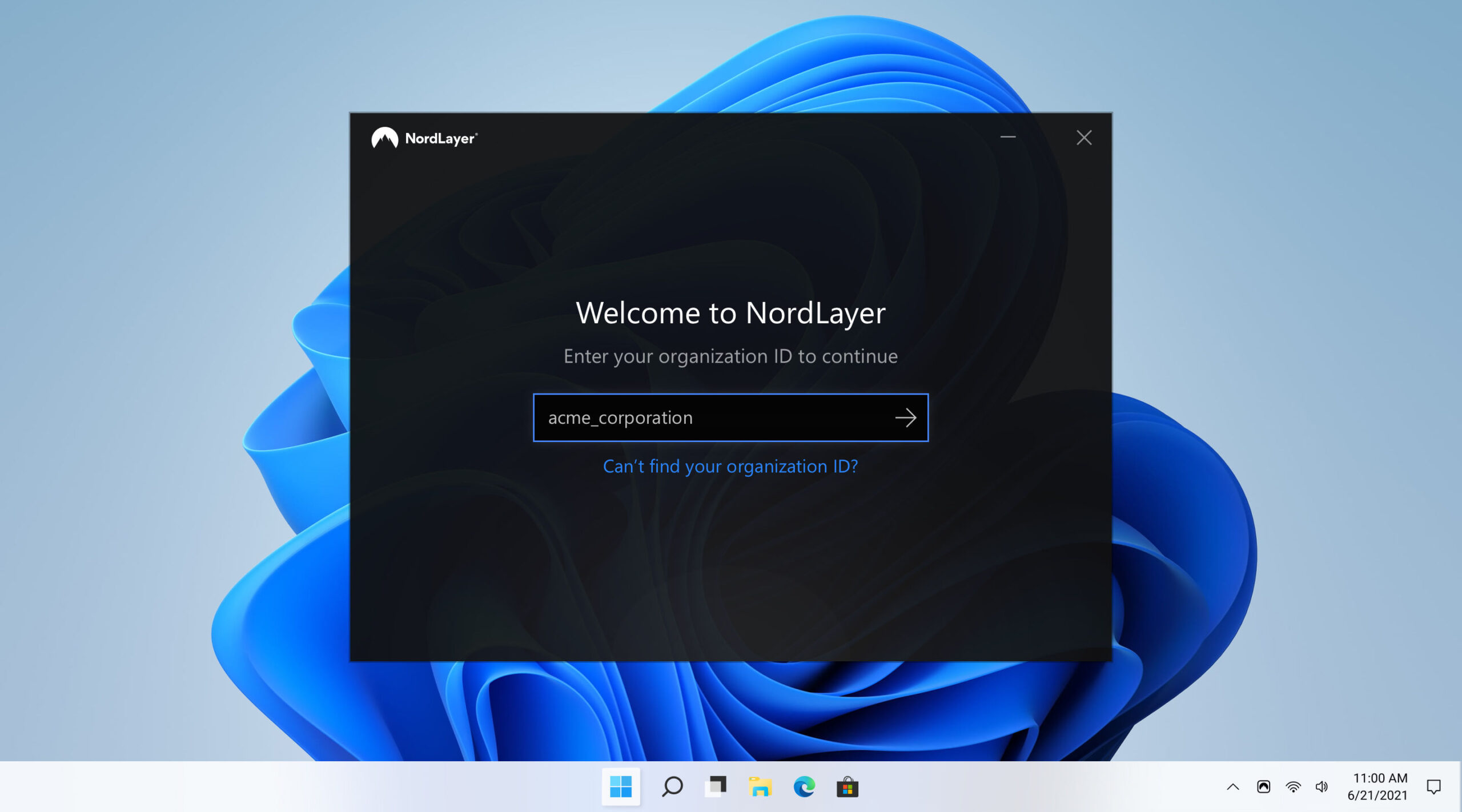
Designed for organizations, NordLayer delivers secure remote access, encrypted traffic, and centralized network control — without the complexity of legacy enterprise VPN setups.
This review explains what NordLayer offers, how it works, and which businesses benefit most.
Why Businesses Need Modern Network Access Control
Remote and hybrid work models have permanently changed security requirements.
Traditional VPNs were built for static office environments. Modern companies now face risks such as:
- Unsecured home networks
- Unauthorized access attempts
- Compromised employee credentials
- Shadow IT usage
- Lack of centralized visibility
Without proper access control, sensitive business systems can be exposed.
Modern network security focuses on:
- Encrypted employee connections
- Controlled access to internal resources
- Network segmentation
- Identity-based access policies
This approach reduces attack surfaces and improves oversight.
What NordLayer Delivers
NordLayer is a business-oriented network security solution built around secure access principles.
It provides:
- Encrypted remote access for employees
- Centralized user management
- Access control policies
- Dedicated business servers
- Secure gateway infrastructure
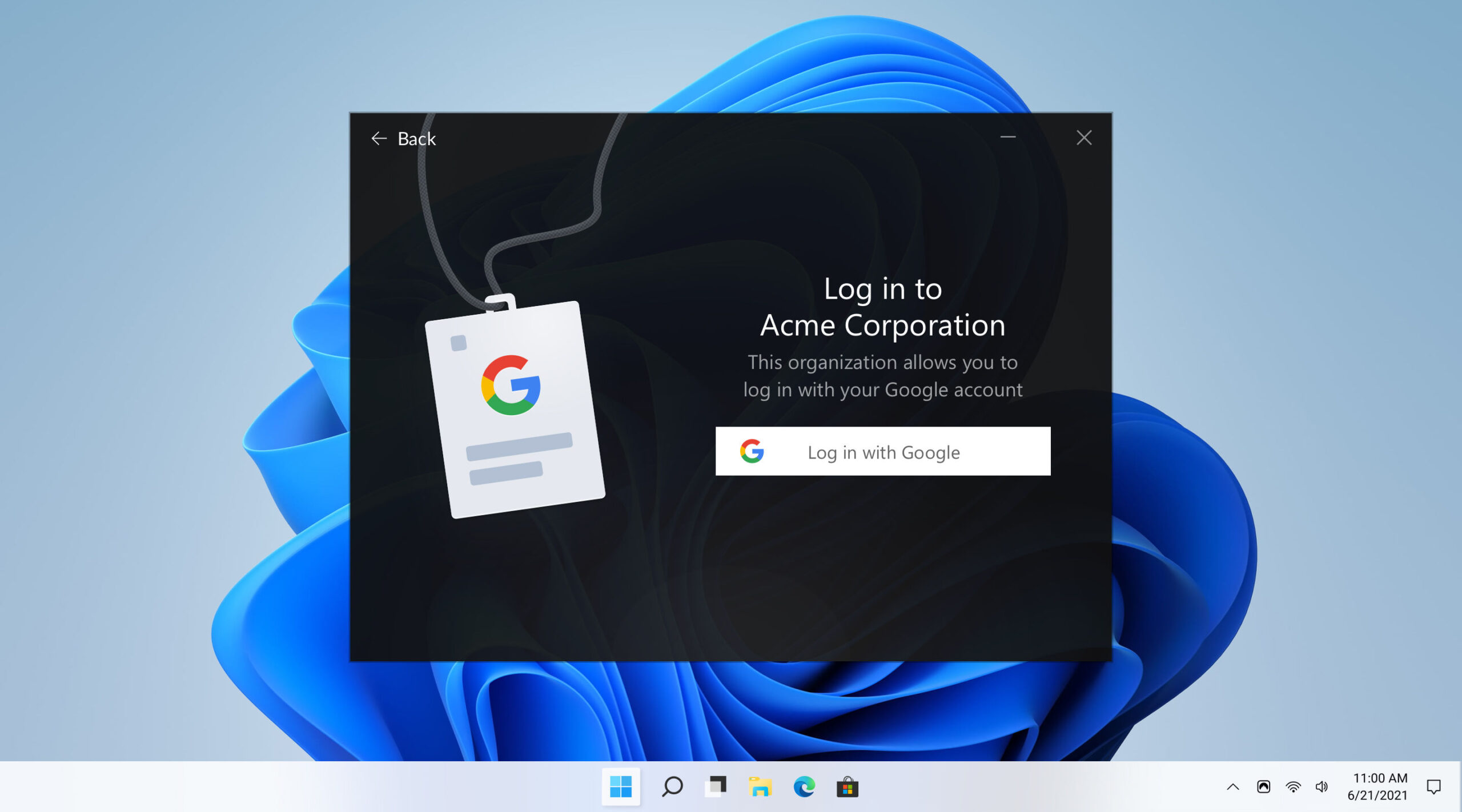
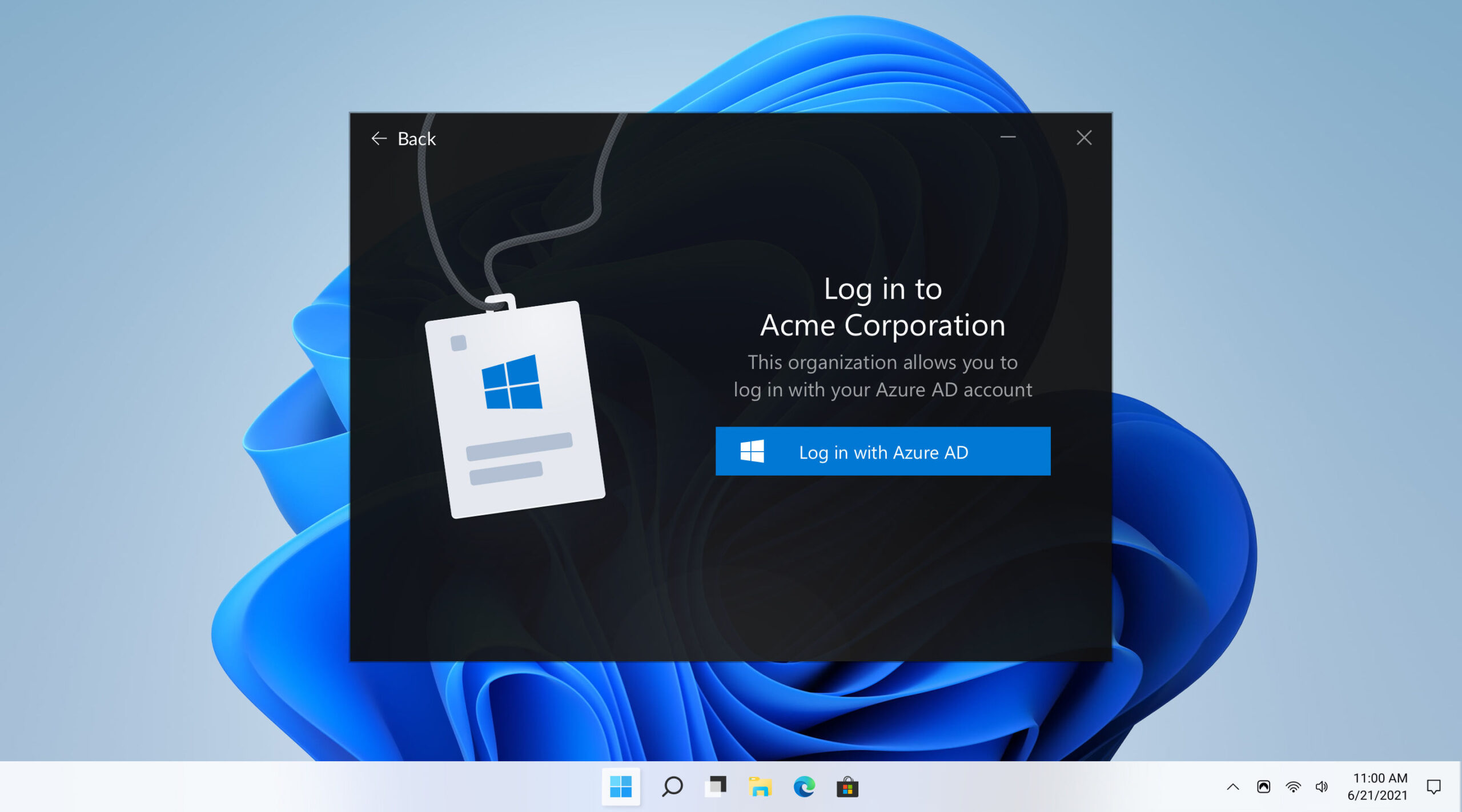
Instead of relying on traditional perimeter security, NordLayer supports a Zero Trust-style access model — verifying identity before granting access to company resources.
🔐 Encrypted Remote Access
All employee traffic routed through NordLayer is encrypted.
This protects:
- Company systems
- Internal communication
- Sensitive cloud services
- Shared databases
Even when employees connect from unsecured networks.
🖥️ Centralized Access Management
IT administrators can:
- Add or remove users
- Assign permissions
- Restrict access by role
- Monitor connection activity
This reduces unauthorized access and simplifies onboarding/offboarding processes.
🌍 Dedicated Servers & Secure Gateways
NordLayer offers business-dedicated infrastructure options, allowing organizations to:
- Maintain consistent IP addresses
- Segment internal traffic
- Improve compliance alignment
- Separate departments or teams
This supports scalability as companies grow.
Pros & Cons
✅ Pros
- Built specifically for organizations
- Centralized management dashboard
- Encrypted remote access for distributed teams
- Supports access control and segmentation
- Scalable for growing companies
❌ Cons
- Not intended for personal VPN use
- Requires internal IT oversight for optimal deployment
- Advanced features may exceed the needs of very small teams
Who Should Use NordLayer?
NordLayer is ideal for:
- Remote-first or hybrid companies
- Businesses with distributed teams
- Organizations handling confidential client data
- Companies seeking Zero Trust-style access control
- IT teams wanting centralized visibility
It may not be necessary for:
- Individual users
- Freelancers without shared infrastructure
- Companies with no remote access requirements
Final Verdict
If your organization needs encrypted remote access, centralized control, and scalable infrastructure without building a complex VPN environment from scratch, NordLayer provides a practical business-focused solution.


