Threat Intelligence with NordStellar – Enterprise-Grade Dark Web & Risk Monitoring
Modern cyber threats don’t start inside your network.
They start outside it.
Leaked credentials, exposed databases, impersonation attempts, and dark web activity often appear long before a company realizes it’s at risk.
That’s where NordStellar comes in.
Built as a threat intelligence and external risk monitoring platform, NordStellar helps organizations detect exposure early, reduce attack surfaces, and respond before incidents escalate.
This review breaks down what it does, how it works, and who it’s built for.
Why External Threat Intelligence Is Critical for Enterprises
Traditional cybersecurity tools focus on internal infrastructure:
- Firewalls
- Endpoint protection
- Network monitoring
- SIEM systems
But many modern breaches originate from:
- Stolen employee credentials
- Third-party data leaks
- Exposed company databases
- Dark web marketplace listings
- Brand impersonation attempts
By the time attackers attempt access, the data may have already been circulating externally.
External threat intelligence shifts the focus outward.
Instead of waiting for a breach to occur, organizations gain visibility into:
- Compromised credentials linked to corporate domains
- Mentions of company assets on dark web forums
- Leaked internal data
- Emerging risks tied to suppliers or partners
Early detection reduces response time — and response time directly impacts financial and reputational damage.

What NordStellar Delivers for Security Teams
NordStellar is designed for cybersecurity professionals, risk analysts, and enterprise decision-makers.
It provides structured intelligence rather than raw data dumps.
Core capabilities include:
- Dark web monitoring for corporate domains
- Credential exposure tracking
- Data leak intelligence
- Brand and asset monitoring
- Risk visibility dashboards
The goal isn’t just awareness.
It’s actionable intelligence.
When exposure is detected, teams can:
- Force credential resets
- Strengthen access controls
- Investigate third-party compromise
- Mitigate reputational damage
- Escalate incidents before exploitation
This reduces dwell time and limits breach impact.
🔎 Dark Web & Marketplace Monitoring
NordStellar scans underground forums, marketplaces, and leak repositories for:
- Corporate email addresses
- Employee credentials
- Sensitive organizational data
- Mentions of company infrastructure
This provides early insight into threat actor activity.
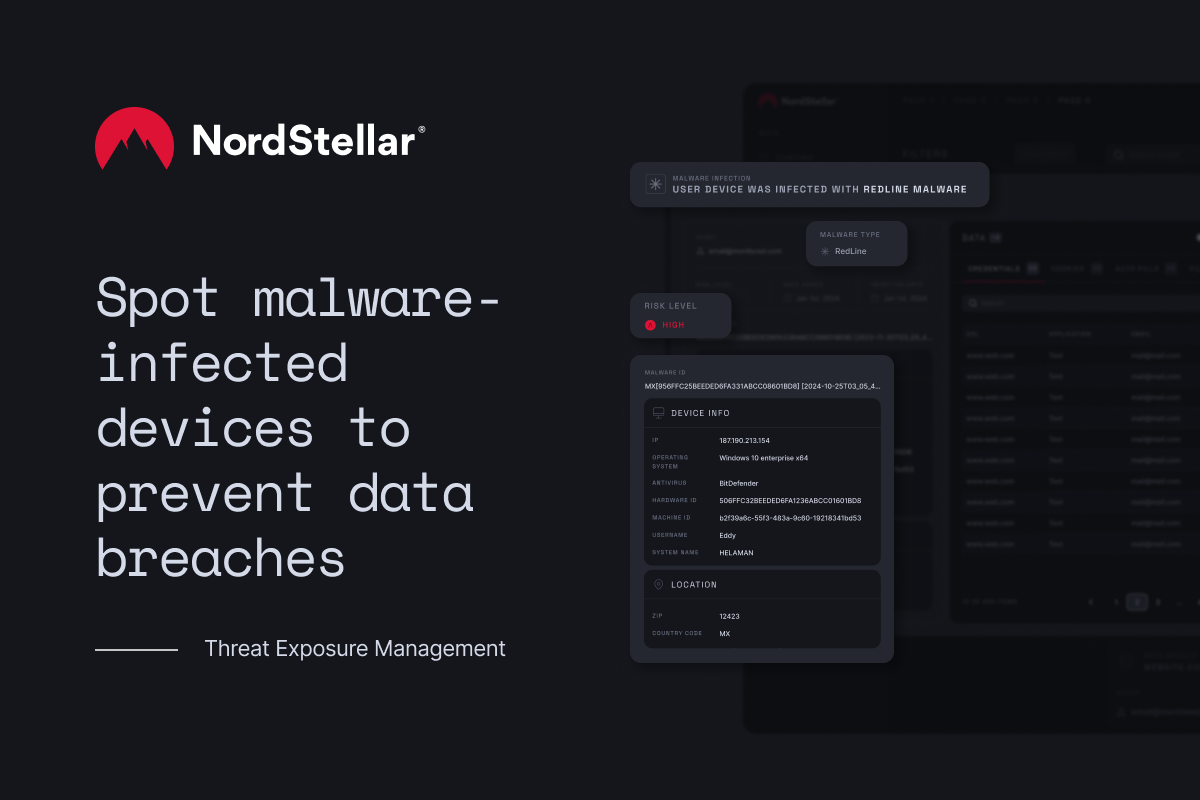
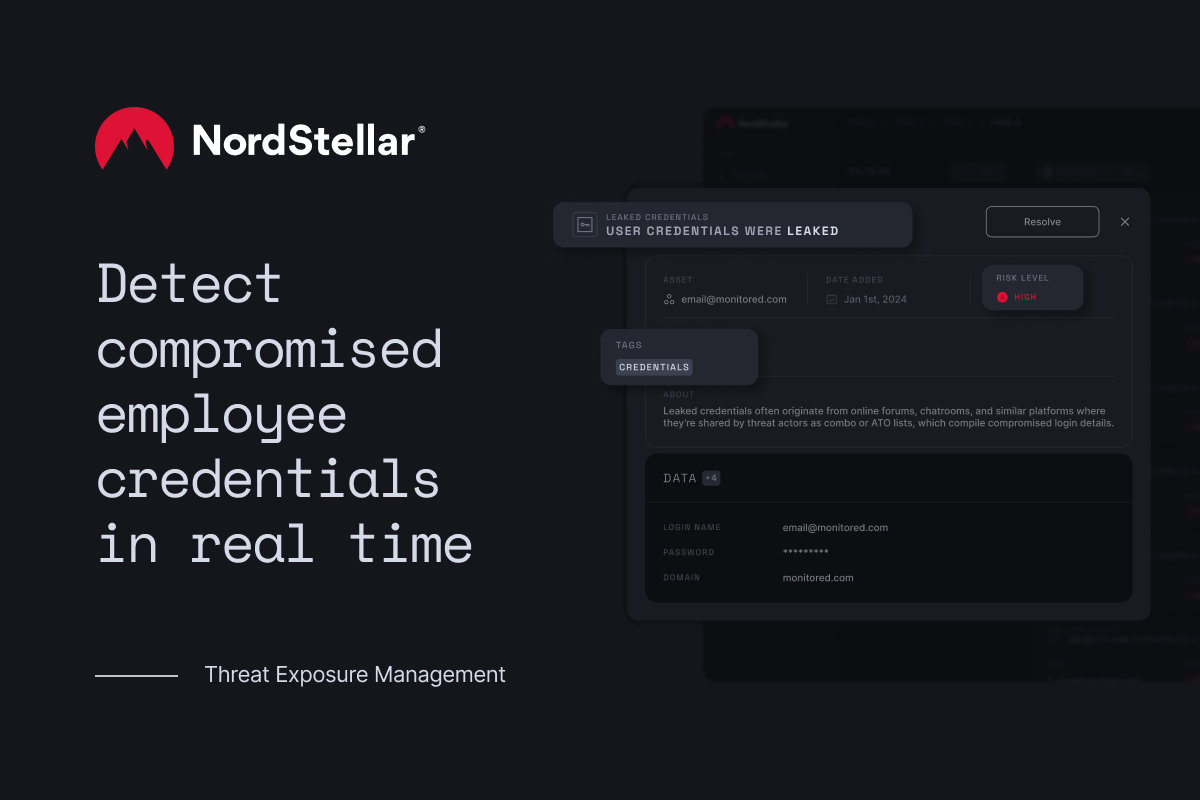
🚨 Credential & Data Leak Intelligence
Stolen credentials remain one of the leading causes of enterprise breaches.
NordStellar helps identify:
- Compromised employee logins
- Password reuse risks
- Newly leaked databases containing company data
This allows immediate remediation before lateral movement occurs.
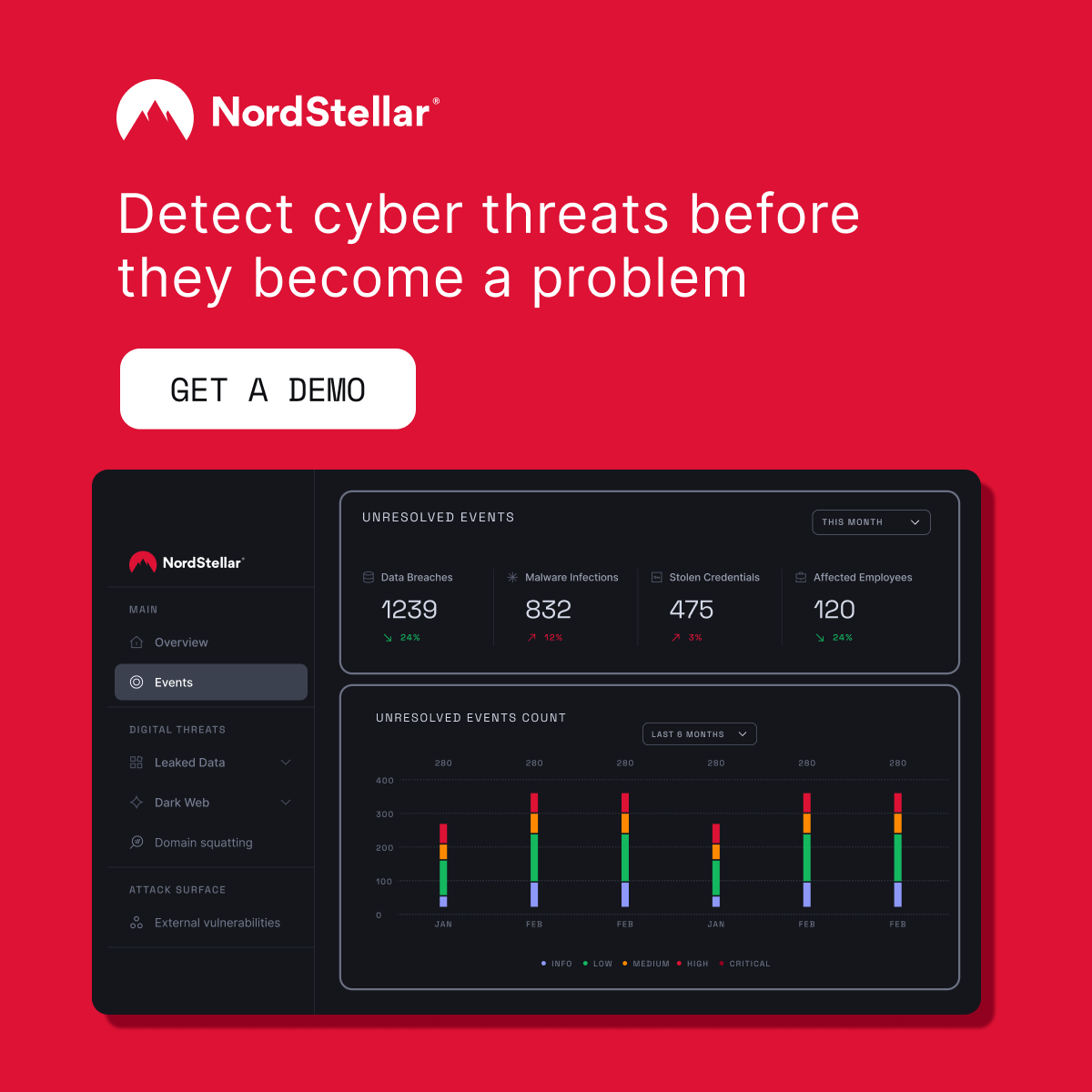
📊 Centralized Risk Visibility
Security teams need clarity — not noise.
NordStellar presents findings through structured dashboards, helping organizations:
- Prioritize risks
- Identify exposure patterns
- Track remediation progress
- Report findings to leadership
This makes it easier to align security efforts with executive-level risk management.

Pros & Cons
✅ Pros
- Enterprise-focused threat intelligence platform
- Dark web and breach monitoring at scale
- Actionable exposure alerts
- Supports proactive risk mitigation
- Clear dashboards for security teams and leadership
❌ Cons
- Designed for businesses, not individual users
- Requires internal security processes for full effectiveness
- Best utilized alongside existing cybersecurity infrastructure
Who Should Consider NordStellar?
NordStellar is ideal for:
- Mid-sized to large enterprises
- Organizations handling sensitive customer data
- Security operations centers (SOC teams)
- Companies concerned about brand abuse or impersonation
- Businesses with regulatory compliance requirements
It may not be suitable for:
- Individual consumers
- Small teams without security oversight
- Organizations without an internal response process
Final Verdict
They surface externally — in leaked databases, credential dumps, and underground forums.
If your organization wants visibility beyond its firewall and the ability to act before damage spreads, NordStellar provides structured, enterprise-grade threat intelligence.